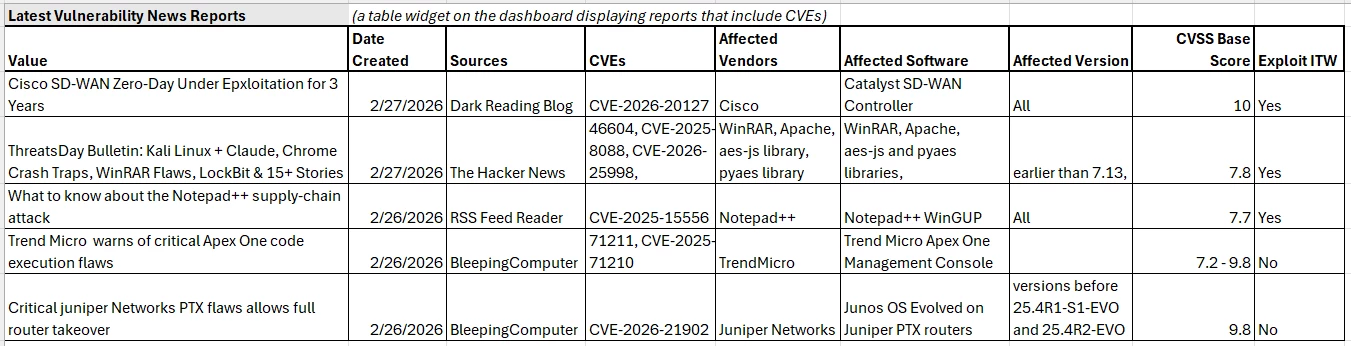
I have a ton of open and closed sources feeding reports, vulnerabilities & CVE indicators into ThreatQ. Because “reports”, “vulnerabilities”, and “indicators” are all different threat libraries inside of ThreatQ, I’ve struggled to find a way to display the amalgamated vulnerability intelligence in one consolidated view that the vulnerability management team can use to track what matters.
I have mocked up the utopian version of what I want to display. How do I create this for real in ThreatQ? All of the data currently exists in ThreatQ, but it’s spread across the three different threat libraries, and none of it exists in all 3 simultaneously.
This seems potentially possible using workflows where you would parse out the CVEs from each report, then append the attributes from the indicator and vulnerability threat libraries into the report. But I don’t know if that’s possible or how I would achieve this.