Here’s what happened...
While browsing a legitimate Formula 1 news site, a programmatic ad creative hijacks your browser session and redirects to a sophisticated social engineering operation impersonating McAfee. The attack chain traversed multiple supply-side platforms (SSPs), a demand-side platform (DSP), and Cloudflare infrastructure before landing on a multi-step scam funnel that used fake virus scans, fabricated threat alerts, an alarm sound, a fake "AI assistant" chat, and an urgency countdown timer — all to drive the victim into purchasing a real McAfee antivirus subscription through a fraudulent affiliate link.
This post documents the complete kill chain from initial ad impression to final monetization endpoint, including extracted IOCs, infrastructure analysis, and the social engineering techniques employed.
The Initial Redirect
The attack began on racingnews365.com, a well-known F1 racing news site. While browsing on a mobile device, Azerion's ad loader served a programmatic display ad that immediately fired a forced redirect, navigating the browser away from the publisher site and onto a scam landing page.
The redirect URL was packed with forensic artifacts that revealed the entire ad supply chain involved in delivering the malicious creative:
https://hidemytrack.site/page0314/v2/android.php
?os=Android
&device=Galaxy%20S20%20Ultra%205G
&cep=[base64url-encoded blob]
&lptoken=175e733f70e304d426f2
&platform=mediasmart_h
&token=1773698624-69721
&bundle=unknown
&domain=racingnews365.com
&placement=513765
&ssp=improve
Every parameter tells a piece of the story:
ssp=improve— the impression was auctioned through Improve Digital, a supply-side platform owned by Azerionplatform=mediasmart_h— the malicious buyer purchased the impression through Mediasmart, a demand-side platform, via a header-bidding integration (_h)domain=racingnews365.comandplacement=513765— the specific publisher and ad slot where the creative rendereddevice=Galaxy S20 Ultra 5G— the victim's device model, parsed from the User-Agent and used to customize the scam luretoken=1773698624-69721— the first segment is a Unix epoch timestamp (2026-03-14T18:43:44Z), pinpointing exactly when the redirect firedcep=— a large base64url-encoded payload containing the full impression context, used by the scam operator's traffic distribution system (TDS) to validate that visitors arrived through a real ad impression
Multiple SSPs, Same Campaign
Continued monitoring revealed a second redirect approximately 3.5 hours later, this time through a different supply path:
https://hidemytrack.site/page0314/v2/android.php
...
&platform=mediasmart_v
&placement=559913616
&ssp=openx
The SSP changed from Improve Digital to OpenX, and the Mediasmart integration changed from _h (header-bidding) to _v (video). The same DSP was bidding on both display and video ad inventory across multiple SSPs — a deliberate strategy to maximize impression volume and diversify the supply chain to avoid single-point takedowns.
A third capture, this time on a different device, revealed a second landing domain — satech-sa.com — with a refined URL structure:
https://satech-sa.com/android/security.php
?brand=LG
&model=Journey%20LTE
&version=Android%2010.0
&cep=[base64url-encoded blob]
&platform=mediasmart_h
&ssp=openx
&domain=racingnews365.com
&placement=559913616
The device parameters evolved from a single device= field to separate brand=, model=, and version= fields — a more granular fingerprint being fed into a newer version of the landing page template.
The Scam Funnel: Seven Steps of Social Engineering
The landing page at satech-sa.com/android/security.php was a meticulously crafted multi-step social engineering funnel impersonating McAfee's brand. The page title declared itself "Android Security - McAfee" and used McAfee's logo and visual identity throughout.
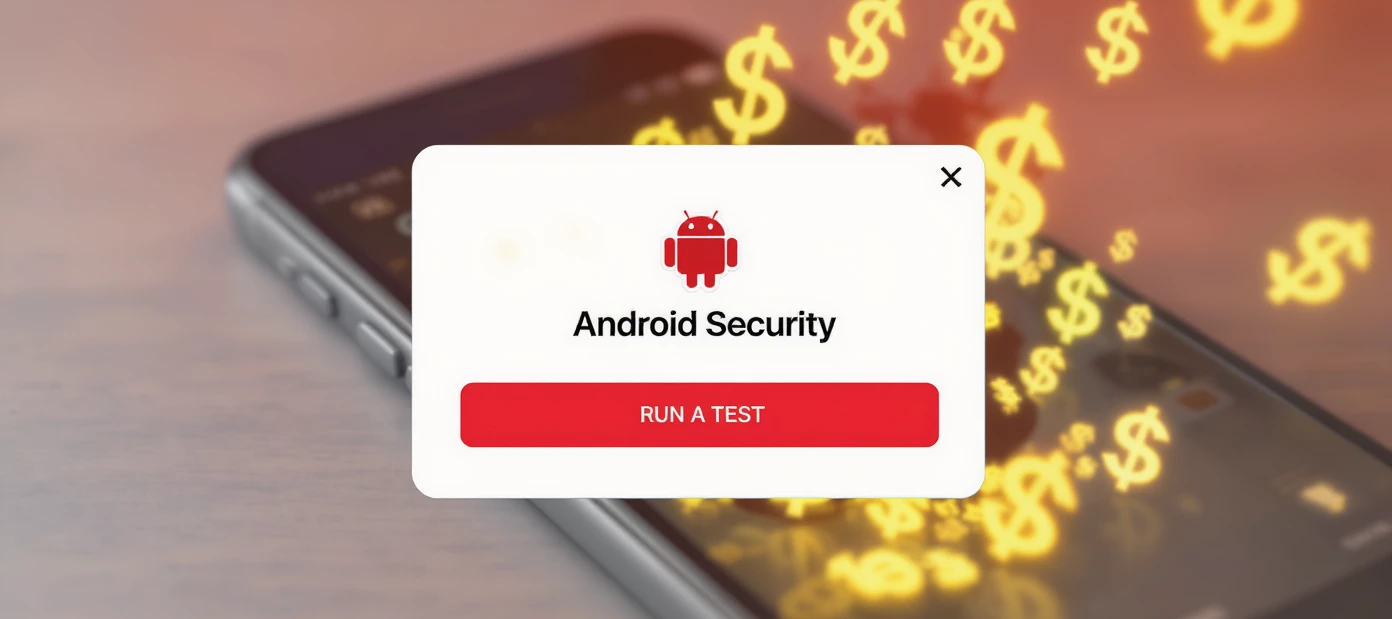
Step 1: Fake System Alert
The initial popup mimicked an Android system dialog overlaid on a fake Android Settings screen background, making it appear as though the alert originated from the operating system itself rather than a browser tab. The device model from the URL parameters was injected directly into the alert text.
[IMAGE 1: Initial popup - "The security system has detected wiretapping on your LG Journey LTE"]
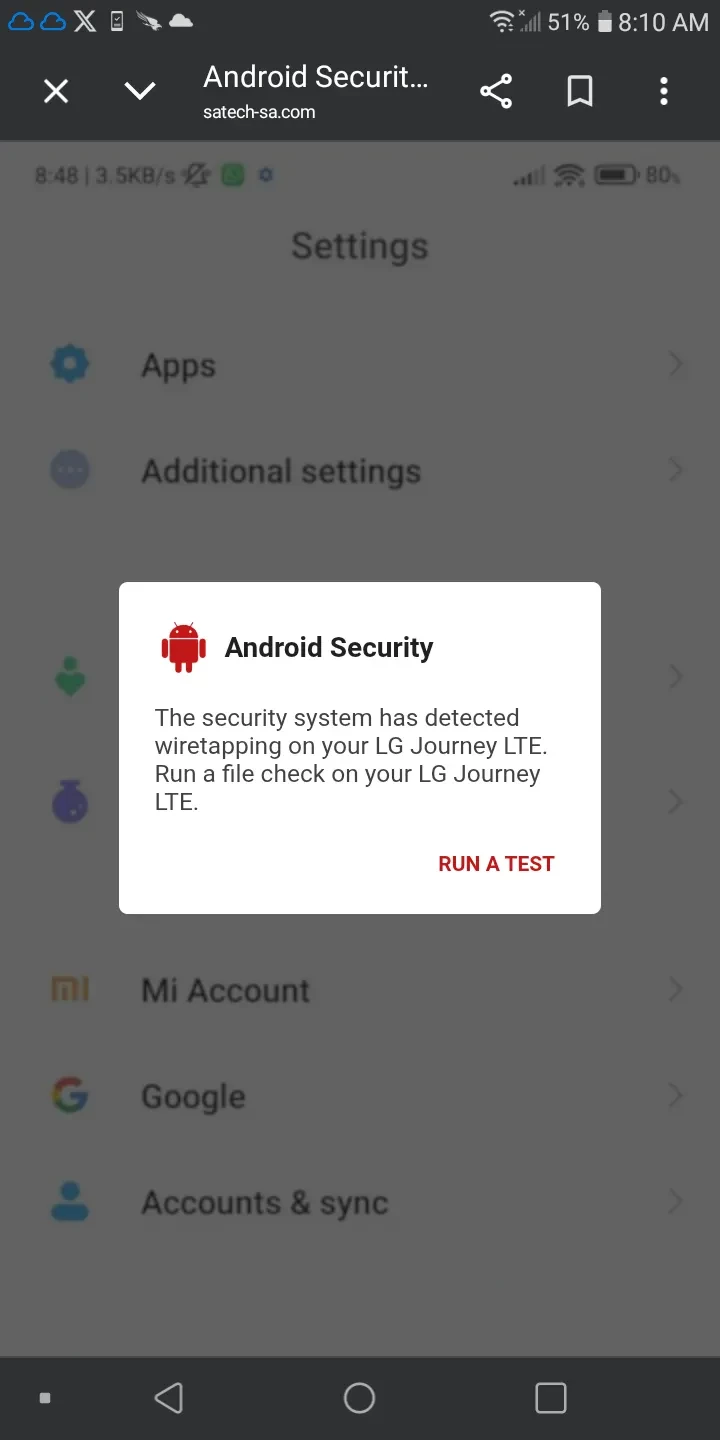
Step 2: Audio Scare and False Choice
Upon tapping "RUN A TEST," an audio file (attention.mp3) played an alarm sound through the phone's speaker. The page then presented two buttons: "Yes, I hear a strange sound" and "I don't hear any sounds." Both paths continued through the funnel — the choice is illusory, designed to create a sense of victim participation and validation.
[IMAGE 2: Audio scare step - "Android has detected wiretapping on your phone!"]
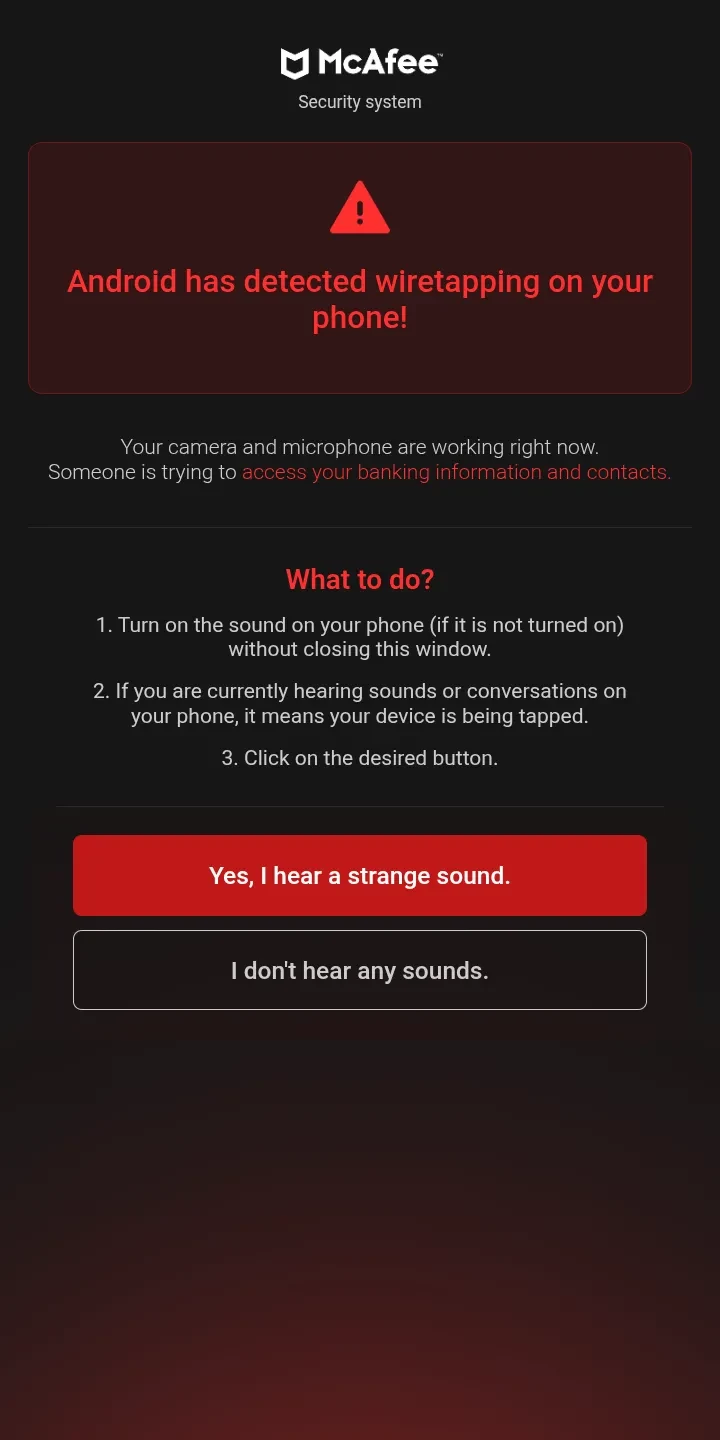
Step 3: Fake Device Scan
The page displayed a simulated McAfee antivirus scan with an animated progress bar, incrementing file counter, and fabricated threat discoveries. The scan "found" five threats including:
../android/trojan..B430014../android/app/tracking_sensor../android/media/spy_wi01041
The victim's real IP address and approximate geolocation were populated via a client-side call to ipapi.co, adding a layer of false credibility. The page also displayed "Camera: ACTIVE," "Microphone: STREAMING," and "Session: root-acces @ surveillance."
[IMAGE 3: Fake antivirus scan results showing 5 fabricated threats]
Step 4: Fake AI Chat
After the scan, a "McAfee Assistant AI" activated, presenting a simulated chatbot that asked three leading questions: "Have you noticed that your device heats up quickly?", "Have you noticed that your device freezes periodically?", and "Have you noticed that your battery is draining faster?" These are universal device behaviors that nearly every smartphone user would recognize, designed to make the victim feel their symptoms match the "diagnosis."
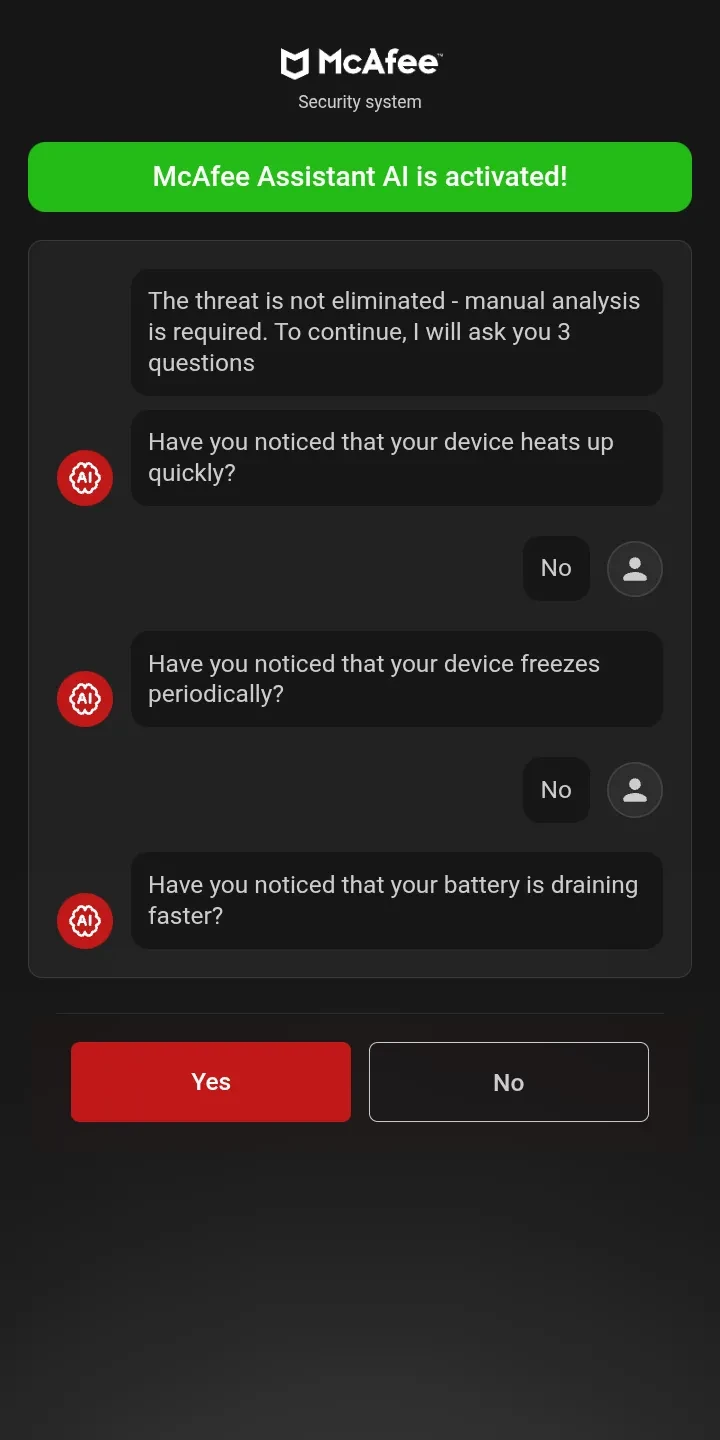
[IMAGE 4: Fake McAfee AI Assistant chat with leading questions]
Step 5: Urgency and Countdown Timer
The final scare screen displayed "Antivirus protection expired on [today's date]!" with a 10-minute countdown timer and the message "Time left before your device is blocked." The expiration date was dynamically generated via JavaScript using the current date, ensuring it always appeared fresh.
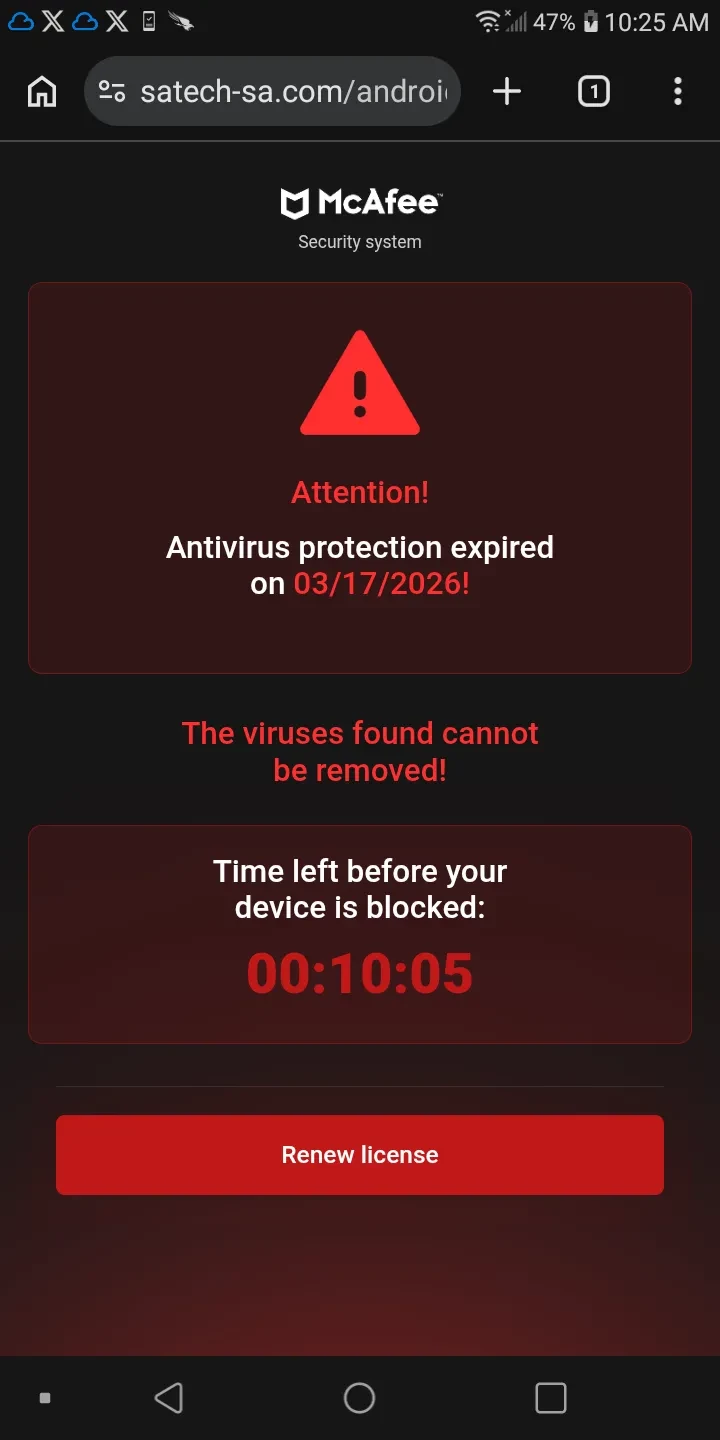
[IMAGE 5: Urgency countdown - "Antivirus protection expired on 03/17/2026!"]
Step 6: The Conversion — "Renew License"
The final call-to-action button, "Renew license," linked to:
https://track.topofferlinks.com/click
Step 7: The Real McAfee Purchase Page
The TopOfferLinks affiliate redirect resolved to McAfee's legitimate purchase page at mcafee.com/consumer/..., presenting the McAfee+ Advanced Individual plan at $89.99.
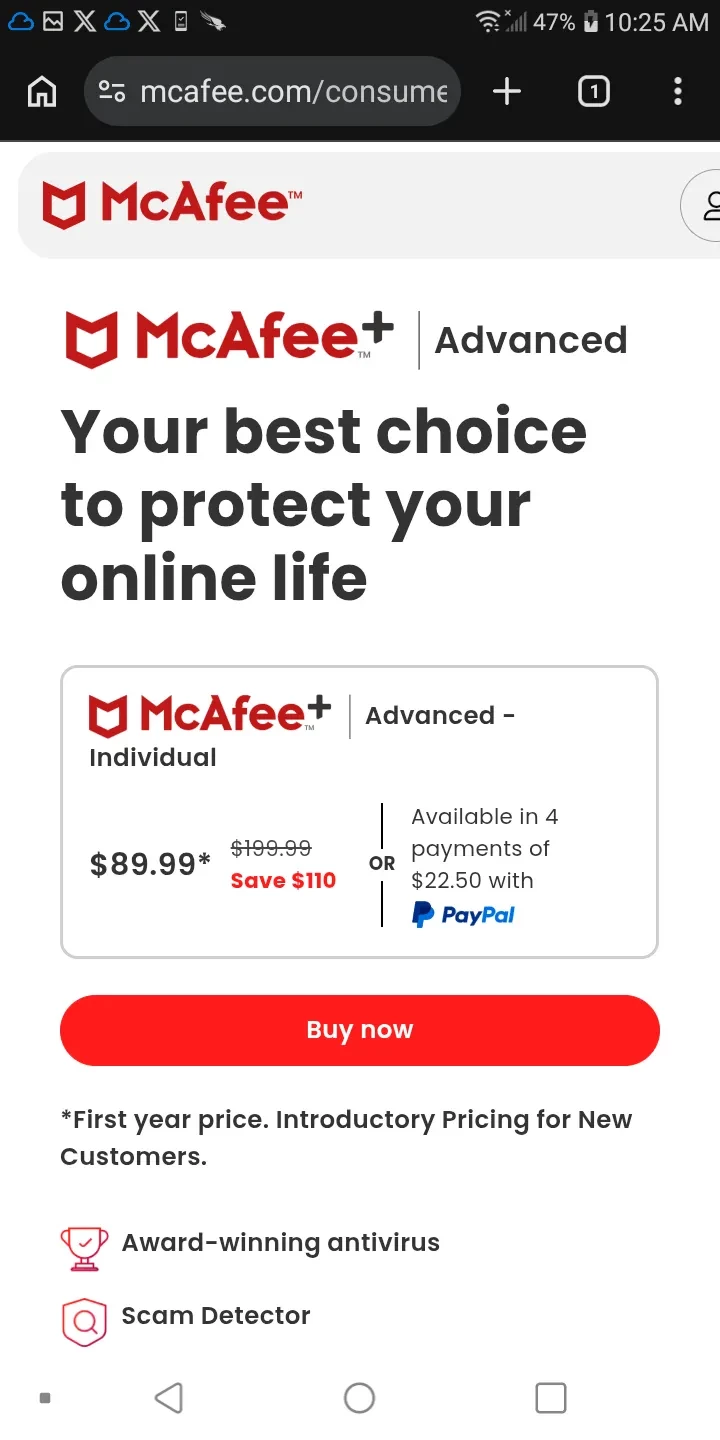
[IMAGE 6: Real mcafee.com purchase page - McAfee+ Advanced Individual at $89.99]
The entire operation — from fake wiretap alerts to fabricated virus scans to AI chatbot manipulation — existed to drive fraudulent affiliate commissions on legitimate McAfee software sales.
Infrastructure Analysis
The scam operation leveraged professional-grade infrastructure across multiple cloud providers:
| Component | Infrastructure | Purpose |
|---|---|---|
| Landing pages | Cloudflare CDN/proxy | DDoS protection, SSL, caching for satech-sa.com |
| Tracking/analytics | AWS CloudFront (d2oy3tinapveug.cloudfront.net) | Operator conversion tracking (ashdia_ namespace) |
| Conversion tracking | Microsoft Ads (bat.bing.com) | UET pixel — suggests cross-platform ad buying |
| Performance monitoring | Akamai mPulse (17de4c14.akstat.io) | RUM analytics on scam pages |
| Geo-gating | ipapi.co | Client-side IP geolocation for victim profiling and content gating |
| Affiliate payout | track.topofferlinks.com | CPA network handling the McAfee affiliate conversion |
| Ad buying | Mediasmart DSP | Programmatic impression purchasing across multiple SSPs |
| Ad supply | OpenX, Improve Digital (Azerion) | SSPs that served the malicious creative |
Operator Attribution
Commented-out JavaScript in the source code contained Russian-language strings:
alert("⚠️ Попытка покинуть страницу зафиксирована. Передача данных продолжится.");
// "An attempt to leave the page has been recorded. Data transfer will continue."
alert("⚠️ Вы свернули страницу. Система останется без защиты.");
// "You minimized the page. The system will remain unprotected."
This code was a back-button trap using history.pushState combined with navigator.vibrate() to physically shake the phone when the victim tried to leave. It was commented out in the deployed version — possibly disabled after testing showed it triggered browser-level warnings — but the Russian-language comments confirm the development language of the operators. This aligns with recent Bitdefender research documenting Slavic-speaking threat actor groups operating structurally similar malvertising campaigns across Meta platforms.
Anti-Analysis and Cloaking
Multiple layers of cloaking and anti-analysis were observed:
- Token validation: The landing page backend validated the
cepparameter andtokentimestamp. Direct URL probing with stale or absent tokens returned empty responses, preventing security researchers from replaying captured URLs. - TLS fingerprint detection: A Playwright-based browser emulator with mobile User-Agent emulation was unable to trigger the malicious ad creative during over an hour of automated monitoring, while a real Android device was served the redirect within minutes. The programmatic ad chain likely validated JA3/JA4 TLS fingerprints to filter non-genuine mobile traffic.
- Geo-gating via
ipapi.co: The client-side geolocation check enabled content gating based on the victim's country or region. - Date-stamped landing pages: The
hidemytrack.sitedomain used daily-rotated paths (/page0314/,/page0315/) to evade blocklist-based detection. - Proxy detection: The scam page failed to load when the device was proxied through mitmproxy for TLS interception, suggesting Cloudflare or the backend performed proxy/MITM detection on the initial page load.
Indicators of Compromise
Network IOCs
| Indicator | Type | Context |
|---|---|---|
hidemytrack.site | Domain | Scam landing domain |
satech-sa.com | Domain | Scam landing domain |
track.topofferlinks.com | Domain | Affiliate conversion redirect |
d2oy3tinapveug.cloudfront.net | Domain | Operator tracking CDN (AWS) |
172.67.223.199 | IPv4 | Cloudflare IP for satech-sa.com |
/android/security.php | URL Path | Landing page endpoint |
/page\d{4}/v\d+/android\.php | URL Pattern | Date-stamped landing pages |
/android/attention.mp3 | URL Path | Scare audio asset |
/jump/render/result | URL Path | Operator conversion tracking endpoint |
Behavioral IOCs
| Indicator | Context |
|---|---|
ashdia_uploadLandpageApearSuccess | JavaScript function name — operator tracking namespace |
ashdia_sendBeaconTrack | JavaScript function name — beacon fallback |
4c9ea758a1cc4db4a587645c5fde7453 | Cloudflare Web Analytics token for scam domain |
data-param="brand" / data-param="model" | HTML attribute pattern for dynamic device injection |
root-acces @ surveillance | Hardcoded fake session string in scan results |
URL Parameter Patterns
Requests matching the following structure indicate involvement in this campaign:
?brand=*&model=*&version=*&cep=*&lptoken=*&platform=mediasmart*&token=*&domain=*&placement=*&ssp=*
Or the older variant:
?os=Android&device=*&cep=*&lptoken=*&platform=mediasmart*&token=*&domain=*&placement=*&ssp=*
Ad Supply Chain Identifiers
| Parameter | Value | Entity |
|---|---|---|
ssp | improve | Improve Digital (Azerion) |
ssp | openx | OpenX |
platform | mediasmart_h | Mediasmart DSP (header-bidding) |
platform | mediasmart_v | Mediasmart DSP (video) |
placement | 513765 | Ad slot on racingnews365.com |
placement | 559913616 | Ad slot on racingnews365.com |
Detection Opportunities
Network-Based Detection (Sigma/Delta)
DNS queries or HTTP requests matching the landing domain patterns, particularly when preceded by navigation to a legitimate news/media site, are strong indicators of this campaign:
title: Malvertising Redirect - Fake McAfee Scam Landing Page
status: experimental
description: Detects navigation to known malvertising scam domains used in fake McAfee campaign
logsource:
category: proxy
detection:
selection_domains:
c-uri|contains:
- 'hidemytrack.site'
- 'satech-sa.com'
selection_patterns:
c-uri|re: '/page\d{4}/v\d+/android\.php'
selection_params:
c-uri|contains|all:
- 'platform=mediasmart'
- 'ssp='
- 'cep='
condition: selection_domains or selection_patterns or selection_params
level: high
tags:
- attack.initial_access
- attack.t1189
Endpoint-Based Detection
Monitor for rapid domain transitions from known media/news publishers to unrelated .site or .com TLDs with heavy query string parameters — a characteristic behavioral signature of forced ad redirects.
Recommendations
- For end users: If you encounter a "virus detected" or "wiretap detected" popup while browsing, close the browser tab immediately. Legitimate security software does not alert you through web browser popups. No website can scan your device for viruses.
- For publishers: Audit your ad supply chain partners, particularly programmatic integrations through SSPs. Implement client-side ad quality monitoring to detect forced redirects from ad iframes.
- For SSPs/DSPs: The Mediasmart DSP account purchasing these impressions should be investigated and suspended. The creative ID associated with placements 513765 and 559913616 on racingnews365.com should be blocklisted.
- For McAfee: The affiliate account routing through
track.topofferlinks.comis generating sales through brand impersonation and fabricated threat scams. Commission clawbacks and affiliate termination are warranted.
Conclusion
This investigation documents a complete malvertising kill chain from programmatic ad auction to affiliate fraud monetization. The operation is notable for its professional infrastructure spanning multiple cloud providers, its use of multiple SSPs to diversify supply, its sophisticated anti-analysis cloaking, and the quality of its social engineering — a multi-step funnel that systematically builds fear and urgency before channeling the victim into a legitimate purchase page.
The ultimate irony is that the scam's "Scam Detector" — McAfee itself — is both the disguise and the product. Every dollar a frightened victim spends on McAfee+ Advanced generates revenue for the very operation that terrorized them into buying it.
Disclosures will be submitted to McAfee, OpenX, and Improve Digital (Azerion)