Audience: Security Analysts, SOC Leads, Architects, MSSPs
Product Module: Threat Analytics / Detection Engineering
Last Updated: March 23, 2026
KB ID: KB-20260323-sta-preview
Tags: Securonix, Threat Analytics, SIEM, Microsoft Sentinel, Risk Scoring, Detection Engineering, SOC, Security Analytics
Problem
As security environments grow in scale and complexity, analysts are often overwhelmed by high volumes of alerts with limited context. Traditional SIEM workflows can make it difficult to connect related events across datasets, leading to alert fatigue and slower investigations.
Objective
Provide an early preview of Securonix Threat Analytics (STA) and how it enhances existing SIEM platforms by improving detection quality, prioritization, and investigation workflows.
Overview
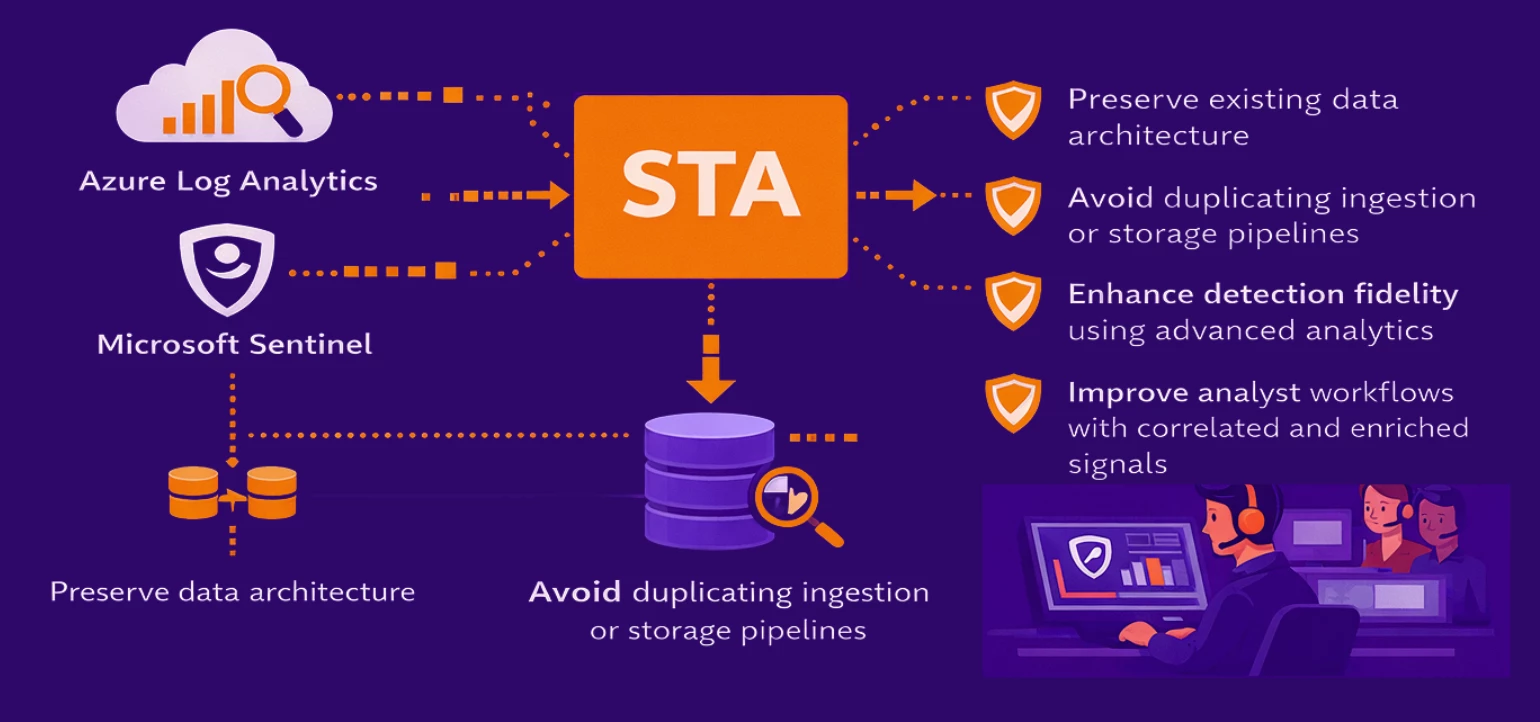
Securonix Threat Analytics (STA) is an advanced analytics layer that operates on top of your existing SIEM and telemetry platforms (such as Microsoft Sentinel).
Rather than replacing your current data infrastructure, STA works downstream, enriching and correlating security data to deliver more meaningful, prioritized insights.
What STA Brings

Architecture Approach
STA is designed to integrate seamlessly with your current data ecosystem.
It leverages data from platforms such as Azure Log Analytics and Microsoft Sentinel without requiring changes to ingestion pipelines or storage architecture.
This approach enables teams to:
Why It Matters
Raw alerts alone are no longer sufficient for modern security operations.
STA shifts the focus from isolated alerts to connected, high-confidence detections, allowing analysts to:

What’s Next
More details on:
-
Architecture patterns
-
Integration workflows
-
Detection and analytics use cases
…will be shared soon in the Securonix Community.
Call to Action
👉 Follow updates here in the Securonix Community to get early access insights and upcoming deep dives on STA.


